Prowler scanner reference for STO
You can scan your configurations and ingest results from Prowler, an open-source tool for performing AWS, GCP and Azure security best practices assessments, audits, incident response, continuous monitoring, hardening and forensics readiness.
Important notes for running Prowler scans in STO
Docker-in-Docker requirements
The following use cases require a Docker-in-Docker background step in your pipeline:
- Container image scans on Kubernetes and Docker build infrastructures
- Required for Orchestration and Dataload scan modes
- Security steps (not step palettes) on Kubernetes and Docker build infrastructures
- Required for all target types and Orchestration/DataLoad modes
The following use cases do not require Docker-in-Docker:
- Harness Cloud AMD64 build infrastructures
- SAST/DAST/configuration scans that use scanner templates (not Security steps)
- Ingestion scans where the data file has already been generated
Set up a Docker-in-Docker background step
-
Go to the stage where you want to run the scan.
-
In Overview, add the shared path
/var/run. -
In Execution, do the following:
-
Click Add Step and then choose Background.
-
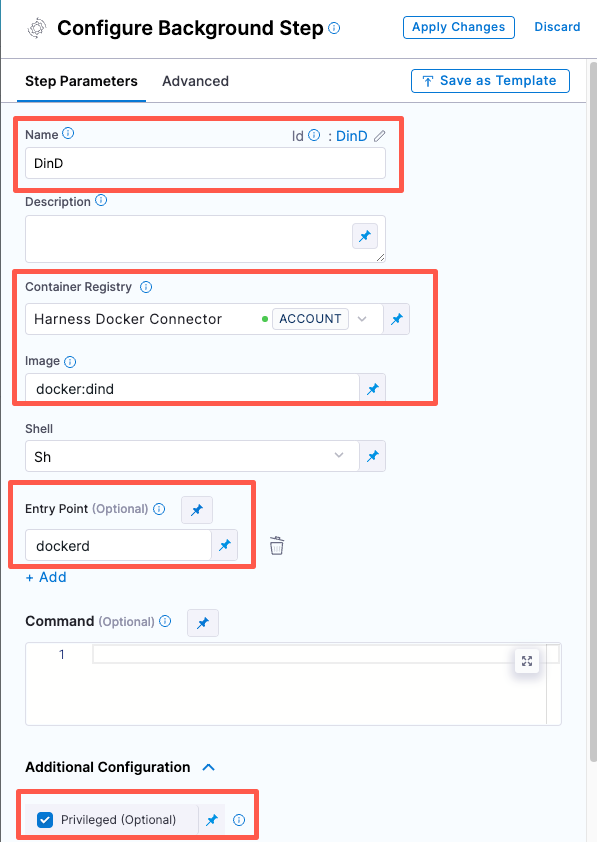
Configure the Background step as follows:
-
Dependency Name =
dind -
Container Registry = The Docker connector to download the DinD image. If you don't have one defined, go to Docker connector settings reference.
-
Image =
docker:dind -
Under Entry Point, add the following:
dockerdIn most cases, using
dockerdis a faster and more secure way to set up the background step. For more information, go to the TLS section in the Docker quick reference.
If the DinD service doesn't start with
dockerd, clear the Entry Point field and then run the pipeline again. This starts the service with the default entry point.- Under Optional Configuration, select the Privileged checkbox.
-
-
- Visual setup
- YAML setup
Add a Background step to your pipeline and set it up as follows:
- step:
type: Background
name: background-dind-service
identifier: Background_1
spec:
connectorRef: CONTAINER_IMAGE_REGISTRY_CONNECTOR
image: docker:dind
shell: Sh
entrypoint:
- dockerd
privileged: true
Root access requirements
You need to run the scan step with root access if either of the following apply:
-
You need to run a Docker-in-Docker background service.
-
You need to add trusted certificates to your scan images at runtime.
You can set up your STO scan images and pipelines to run scans as non-root and establish trust for your own proxies using self-signed certificates. For more information, go to Configure STO to Download Images from a Private Registry.
For more information
The following topics contain useful information for setting up scanner integrations in STO:
Prowler step settings for STO
Scan
Scan Mode
- Orchestration Configure the step to run a scan and then ingest, normalize, and deduplicate the results.
- Ingestion Configure the step to read scan results from a data file and then ingest, normalize, and deduplicate the data.
Scan Configuration
Select the compliance framework to apply when running the scan:
- Default
- Hipaa
- GDPR
- Exclude Extras
Target
Type
- Configuration Scan your cloud environment by gathering configuration data via the cloud provider’s APIs.
Name
The identifier for the target, such as codebaseAlpha or jsmith/myalphaservice. Descriptive target names make it much easier to navigate your scan data in the STO UI.
It is good practice to specify a baseline for every target.
Variant
The identifier for the specific variant to scan. This is usually the branch name, image tag, or product version. Harness maintains a historical trend for each variant.
Workspace
The workspace path on the pod running the scan step. The workspace path is /harness by default.
You can override this if you want to scan only a subset of the workspace. For example, suppose the pipeline publishes artifacts to a subfolder /tmp/artifacts and you want to scan these artifacts only. In this case, you can specify the workspace path as /harness/tmp/artifacts.
Authentication
Settings for the AWS account to use when running an orchestration scan.
Access ID
The username to log in to the scanner.
Access Token
The access token to log in to the scanner. In most cases this is a password or an API key.
You should create a Harness text secret with your encrypted token and reference the secret using the format <+secrets.getValue("project.my-access-token")>. For more information, go to Add and Reference Text Secrets.
Access Region
The AWS region of the configuration to scan.
Ingestion file
The path to your scan results when running an Ingestion scan, for example /shared/scan_results/myscan.latest.sarif.
-
The data file must be in a supported format for the scanner.
-
The data file must be accessible to the scan step. It's good practice to save your results files to a shared path in your stage. In the visual editor, go to the stage where you're running the scan. Then go to Overview > Shared Paths. You can also add the path to the YAML stage definition like this:
- stage:
spec:
sharedPaths:
- /shared/scan_results
Log Level, CLI flags, and Fail on Severity
Log Level
The minimum severity of the messages you want to include in your scan logs. You can specify one of the following:
- DEBUG
- INFO
- WARNING
- ERROR
Additional CLI flags
You can use this field to run the prowler aws scanner with specific command-line arguments. For example, this argument excludes specific checks from a scan: -excluded-checks s3_bucket_public_access
Fail on Severity
Every Security step has a Fail on Severity setting. If the scan finds any vulnerability with the specified severity level or higher, the pipeline fails automatically. You can specify one of the following:
CRITICALHIGHMEDIUMLOWINFONONE— Do not fail on severity
The YAML definition looks like this: fail_on_severity : critical # | high | medium | low | info | none
Additional Configuration
In the Additional Configuration settings, you can use the following options:
Advanced settings
In the Advanced settings, you can use the following options:
Security step settings for Prowler scans in STO (legacy)
You can set up Prowler scans using a Security step, but this is a legacy functionality. Harness recommends that you use an Prowler step instead.
Target and variant
The following settings are required for every Security step:
target_nameA user-defined label for the code repository, container, application, or configuration to scan.variantA user-defined label for the branch, tag, or other target variant to scan.
Make sure that you give unique, descriptive names for the target and variant. This makes navigating your scan results in the STO UI much easier.
You can see the target name, type, and variant in the Test Targets UI:
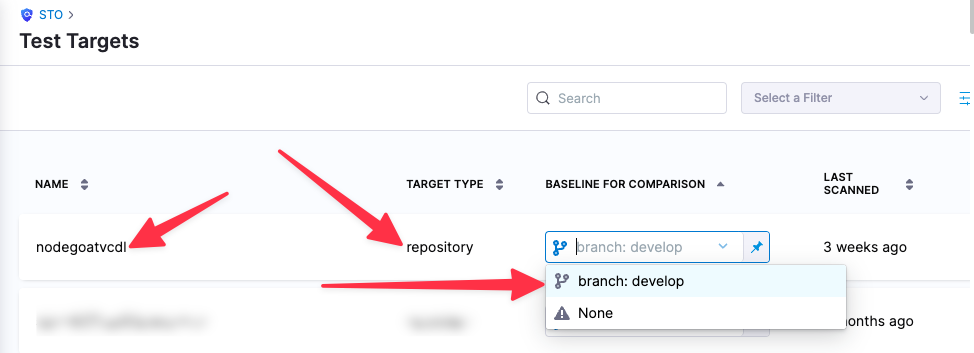
For more information, go to Targets, baselines, and variants in STO.
Prowler scan settings
product_name=prowlerscan_type=configurationpolicy_type=orchestratedScanoringestionOnlyproduct_config_name- Accepted values(s):
default,hipaa,gdpr,exclude_extras
- Accepted values(s):
fail_on_severity- See Fail on Severity.tool_args— You can use this field to run the prowler aws scanner with specific command-line arguments. For example, the following argument excludes a specific check from a scan:tool_args=-excluded-checks s3_bucket_public_access
Configuration scan settings
The following settings apply to all scanners where the scan_type is configuration. You should create Harness text secrets with your encrypted access ID and token and access them using the format <+secrets.getValue("project.my-secret")>.
configuration_type- accepted value(s)s:
aws_account
- accepted value(s)s:
configuration_regionconfiguration_environmentconfiguration_access_idconfiguration_access_token
Ingestion file
If the policy_type is ingestionOnly:
ingestion_file= The path to your scan results when running an Ingestion scan, for example/shared/scan_results/myscan.latest.sarif.
-
The data file must be in a supported format for the scanner.
-
The data file must be accessible to the scan step. It's good practice to save your results files to a shared path in your stage. In the visual editor, go to the stage where you're running the scan. Then go to Overview > Shared Paths. You can also add the path to the YAML stage definition like this:
- stage:
spec:
sharedPaths:
- /shared/scan_results